Linux/Windows post-exploitation framework made by linux user
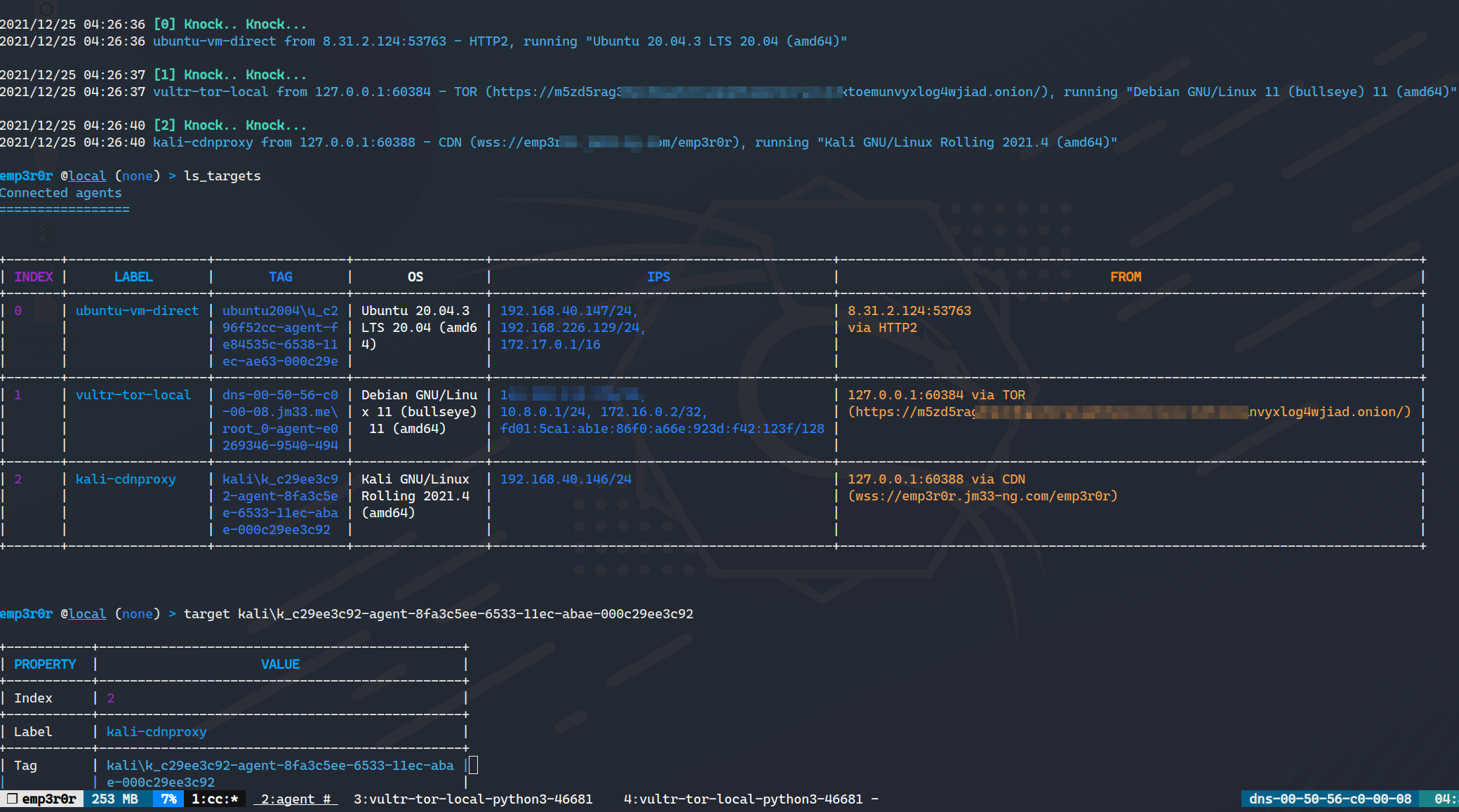
emp3r0r C2 (Linux and Windows) is ready for testing, please report bugs if you find any
- read the wiki to get started
- download from here
- write modules for emp3r0r, with your favorite languages
- Windows support is ready, with fully-interactive shell
emp3r0r was initially developed as one of my weaponizing experiments, i tried to implement common Linux adversary techniques and some of my own ideas, it was a learning process for me
what makes emp3r0r different? well, first of all, its the first C2 framework that targets Linux platform, and you can use basically any other tools through it. if you need more reasons to try it out, check features
emp3r0r also has complete python3.9 support, that is less than 7MB with necessary third party packages such as requests and mysql
- beautiful terminal UI, use tmux for window management
- multi-tasking, you don't need to wait for any commands to finish
- module support: provide python3.9 environment, easily run your exploits/tools on any linux host
- perfect shell experience via SSH, compatible with any SSH client, also available for Windows
- bettercap
- built-in static bash binary
- auto persistence via various methods
- post-exploitation tools like nmap, socat
- credential harvesting (WIP)
- process injection
- shellcode injection
- ELF patcher (WIP)
- packer that encrypts and compresses agent binary, and runs agent in a covert way
- hide processes and files (WIP)
- port mapping, from c2 side to agent side, and vice versa
- agent side socks5 proxy
- auto root
- LPE suggest
- system info collecting
- file management, resumable download/upload
- log cleaner
- screenshot
- stealth connection
- anti-antivirus
- internet access checker
- autoproxy for semi-isolated networks
- reverse proxy to bring every host online
- all of these in HTTP2
- painlessly encapsulated in Shadowsocks and KCP
- can be encapsulated in any external proxies such as TOR, and CDNs
- interoperability with metasploit / Cobalt Strike
- custom modules
- and many more...